2. Select a security server solution
After this section you have
- together with the technical person considered a security server solution and the factors that affect to the decision
Once you have familiarised yourself with the possibilities of the Suomi.fi Data Exchange Layer and planned and resourced its deployment, you can start joining the Data Exchange Layer. The security server connects your organisation's information system(s) to the Data Exchange Layer.
Your organisation must first decide how to implement the Security Server. Once you have selected a security server solution, your organisation must install and configure the host server for the security server.
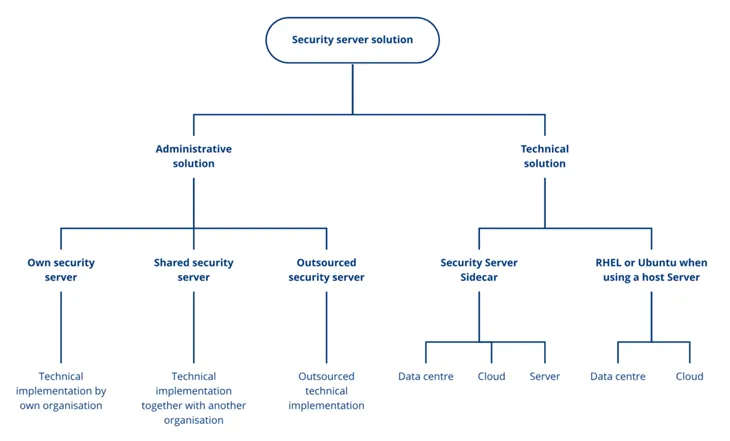
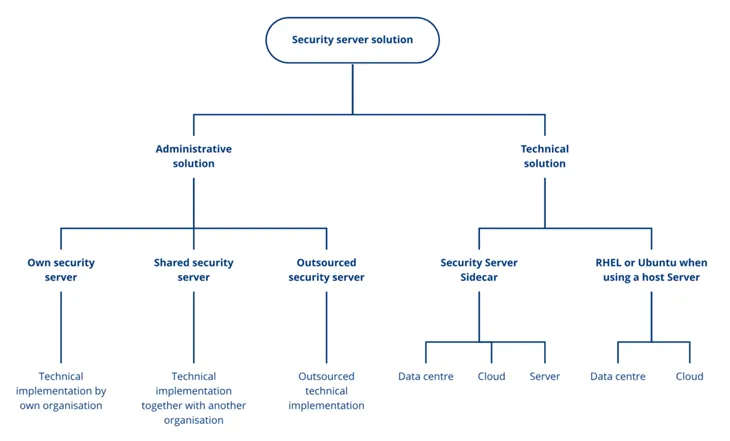
In this chapter we present the phases that are included in the process of the security server solution:
- Choose the implementation method of the security server. Implementation method of the security server can be own, shared or outsourced.
- Install and configure the host server.
1. Choose the implementation method of the security server
Own, shared or outsourced security server?
Own security server
- Enough financial, technological and human resources to install and maintain an own security server
- Enough technical expertise : in security server technologies (RHEL/Ubuntu or Docker) and/or in technologies of the security servers operating environments (AWS and Kubernetes)
- Own use of the Data Exchange Layer is heavy: organisation uses several other services and/or provides own services in the Data Exchange Layer
- Read more about the implementation of a security server from the instructions of the technical deployment process
Shared security server
- An other organisation, that has joined Data Exchange Layer, already has a security server
- Own use of the Data Exchange Layer : is limited – own organisation uses only a few Data Exchange Layer services OR is heavy – it is possible to share the security server if another organisation’s security server has sufficient capacity
- Read the article about sharing a Security Server
Outsourced security server
- Own organisation has not enough technical expertise or resources
- The organisation that provides outsourcing services has existing infrastructure (data centre or cloud)
- Outsourcing is possible regardless of the usage rate of the Data Exchange Layer
- Read the article about outsourcing a Security Server
Factors that affect to the security server solution
Resources
Installing and maintaining your own security server requires financial, technological and human resources. Not all organisations should install their own security server. Sharing a security server is a good choice for organisations that are in the same industry and work together a lot, for example. When a Security Server is shared with another organisation, the costs are also shared, which results in cost savings.
The costs of outsourcing the security server depends on your service provider. Read more about the service providers that provide outsourcing of joining the Data Exchange Layer.
Technical competence
The security server implementation requires technical expertise that is explained in the instructions of the technical deployment process.
Selection of the operating environment
Selection of the operating environment requires knowledge in technologies of the security server’s operating environment which are explained in the instructions of the technical deployment process.
The Data Exchange Layer security servers can be placed either
- within the existing IT infrastructure,
- in a data centre or
- in a cloud environment
When making your choice, consider whether your organisation has an existing IT infrastructure or whether it needs to be purchased separately for the security server. Consider whether acquiring infrastructure is financially sensible or whether sharing or outsourcing the security server would be a better solution.
Also consider how the security server will be used. If the usage is heavy or varies significantly, a cloud service is usually the most cost-effective option and costs will not arise for the use of excess capacity.
Security and data protection requirements
Note that your organisation must consider the operational environment of the security server from the security perspective because security and data protection requirements may impose restrictions on the security server environment. For example, if the data processed in the Data Exchange Layer must stay within the borders of and governed by laws of Finland, the security Server must be located in a Finnish data centre or in a cloud environment located in Finland.
Note that your organisation must consider the security and data protections requirements even if you outsource the implementation of the security server or share the security server with another organisation.
Public administration organisations can take a look at the Ministry of Finance's Guidelines for Public Sector on Data Communications Services (in Finnish)Opens in a new window., for example.
All Data Exchange Layer security server solutions enable secure data processing for your organisation, which is why the security server can be deployed as is. However, if your organisation's data processing requirements are not met, your organisation can implement separate self-defined encryption solutions. Please remember that your organisation must ensure the information security of its own information systems and their integrations.
Usage rate
Your organisations usage rate of the Data Exchange Layer and the way it is used also affect the choice of solution.
If the use of the Data Exchange Layer is limited, i.e. your organisation uses only a few Data Exchange Layer services:
- Consider using another organisation's security server or outsourcing the implementation of the security server, since implementing your own security server may not be cost-effective.
- If your organisation wants to implement its own security server, a containerised security server either on the same server as the e-service or implemented in a cloud environment is often a good and cost-effective solution. Read more about the containerised security server.
If the Data Exchange Layer is used heavily, i.e. your organisation uses several services of the Data Exchange Layer and/or provides services through the Data Exchange Layer.
- Setting up your own security server might be a good option
- It is possible to share the security server of another organisation if that security server has sufficient capacity
- It is also possible to outsource the security server
2. Install and configure the host server
If your organisation implements an own security server, person responsible for the technical deployment of the security server prepares the implementation of a security server solution by following the materials of the technical deployment process instructions and the support articles.