Sharing a security server with another organisation
A security server can be shared between multiple organisations. Sharing results in cost savings when you can share the costs of the security server with other organisations. A security server that uses both RHEL or Ubuntu host server or a Security Server Sidecar can be shared between organisations. Organisations can also purchase a security server together from an external service provider.
When a security server is shared with another organisation, the organisation that owns the security server is responsible for administering it. The responsibilities between the organisations that are sharing the security server depend on the agreement made. Usually, the organisation that owns the security server is mainly responsible for the technical maintenance and the organisation that is joining the security server often just sends the user permit application and creates the client certificate according to the agreement.
As of 6 May 2026, manually renewed certificates used in the Data Exchange Layer are applied for through the Digital and Population Data Services Agency’s (DVV) e-services by the organisation that owns the security server. The owner of the security server applies for all certificates required by that security server, also on behalf of the organisations using the shared security server. Applying for certificates on behalf of other organisations must be agreed between the organisations in advance, and the necessary authorisations must be properly documented.
Shared security server certificates:
- Authentication certificate: Used for authenticating the security server for connections between security servers. If your organisation joins an existing security server, the security server already has an authentication certificate.
- Signing Certificate: Used to sign messages sent by systems. Each organisation has its own Signing Certificate that is used for certifying the messages used by the organisation's own services. The organisation that owns the security server creates the Signing Certificate.
- Internal TLS Certificate: With this certificate, the security server authenticates the information system. Enabled for HTTPS connections, i.e., mandatory when a security server is shared. A Client Certificate is subsystem-specific. Internal TLS Certificate can be created either by an organisation that owns the security server or by the organisation connecting to the security server.
- The security server's own certificate: The information system authenticates the security server by means of a certificate. This is especially important when providing services.
An example of shared security server with another organisation
Municipality is going to join the Data Exchange Layer to get personal record from Population Information System (PIS) of Digital and Population Data Services Agency. Municipality does not have knowledge in Linux and Docker, so organisation decides to join the security server that is administrated by another city that has already joined the Data Exchange Layer. Municipality sends a user permit application to the Data Exchange Layer’s test and production environments and receives security server’s information from the city for the user permit application. City takes care of the technical joining of municipality to the security server and adequate performance of the security server.
How to start using another organisation’s security server
Things to note when using another organisation's security server
If you are using another organisation's security server, make sure that you have made the necessary agreements and have the necessary information to start the deployment process. Remember to arrange and agree on security server policies, such as the creation of an Internal TLS Certificate.
Phases for starting to use another organisation’s security server
- Make an agreement with the other organisation on the use of their security server.
- Fill in the user permit application. For the user permit application, you need the security server name (FQDN), IPv4 address, and the organisation class (GOV, MUN, COM, PRI, EDU) of the organisation that owns the security server.
- The technical implementation is carried out by the organisation that owns the security server.
What to do when another organisation wants to use your organisation's security server?
Things to note when sharing a security server
- Technical requirements, performance and memory configuration of a security server: If the security server needs to process a large number of queries, consider using an external load balancer.
- Renewal of certificates: Remember that you are also responsible for renewing the Signing Certificates of the other organisation.
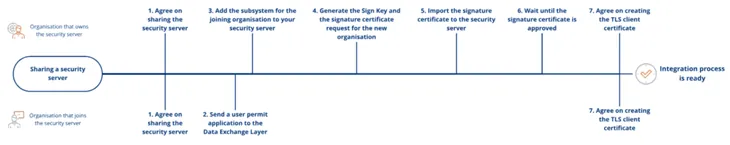
Phases to add another organisation's subsystem to your security server
- The joining organisation must have permission to use your existing security server. Your organisation and the other organisation must agree on this together.
- The joining organisation will send a user permit application to the Data Exchange Layer. Once the Data Exchange Layer’s Maintenance team has received and processed the application, the organisation and its subsystem are added to the central server.
- When that has been done, the Data Exchange Layer’s Maintenance team will prompt you to add the subsystem for the joining organisation to your security server. Add the subsystem.
- Create a signing key (Sign Key) and a signing certificate request for the connecting organisation in the security server’s management interface. The organisation that owns the security server applies for the signing certificate via DVV’s e-services using its own customer account and attaches the created certificate request to the application. Applying for certificates on behalf of other organisations must be agreed in advance, and the necessary authorisations must be properly documented.
- DVV delivers the signed certificate to the technical contact person specified in the certificate application. The security server administrator installs the signing certificate on the security server and confirms to the connecting organisation when the certificate has been taken into use.
- The Data Exchange Layer’s Maintenance team will approve the registration of the signature certificate on the central server.
- TLS client certificate must be created for the associated organisation. You can either create a certificate yourself or ask the joining organisation to create and send the completed certificate back to you. The generated client certificate is used by the server administrator to encrypt the connection between the client system and the subsystem.
- You have now succesfully added another organisation to your security server